Infrastructure Testing in Kubernetes
Table of Contents
The problem
Kubernetes infrastructure failures don't announce themselves. A misconfigured network policy, an exhausted resource quota, a drifting storage configuration. These issues are invisible until something breaks in production, and by then, the blast radius has already expanded across multiple workloads.
The challenge is scope. Infrastructure testing in Kubernetes spans cluster health, compute resources, networking, and storage, each requiring different tools and validation approaches. Teams cobble together scripts using curl, pytest, k6, and custom checks, but without a unified framework, these efforts become fragmented and hard to maintain. Tests live in different repos, run on different schedules, and produce results that nobody aggregates.
The result: teams either skip infrastructure testing entirely (and accept the risk) or invest significant engineering time building and maintaining custom validation pipelines that weren't designed for Kubernetes-native environments.
The solution
Testkube provides a cloud-native, vendor-agnostic framework for orchestrating infrastructure tests directly inside your Kubernetes clusters. Instead of managing scattered scripts and tools, teams define infrastructure validations as Test Workflows that run natively in Kubernetes using the tools they already know.
Key capabilities
- Orchestrate multi-step infrastructure validations combining curl, pytest, k6, and custom tools into a single workflow
- Run tests at strategic points: pre-deployment, post-upgrade, on a schedule, or as quality gates before critical releases
- Execute tests inside your cluster for accurate results without exposing infrastructure externally
- Centralize all results, logs, and artifacts in a single dashboard regardless of which tool or trigger initiated the test
- Scale validation across clusters, environments, and geographies from a single control plane
How it works
- Define your validation workflows using Testkube's Test Workflow format. Combine familiar tools (curl for health checks, k6 for load testing, pytest for custom assertions) into sequenced or parallel steps.
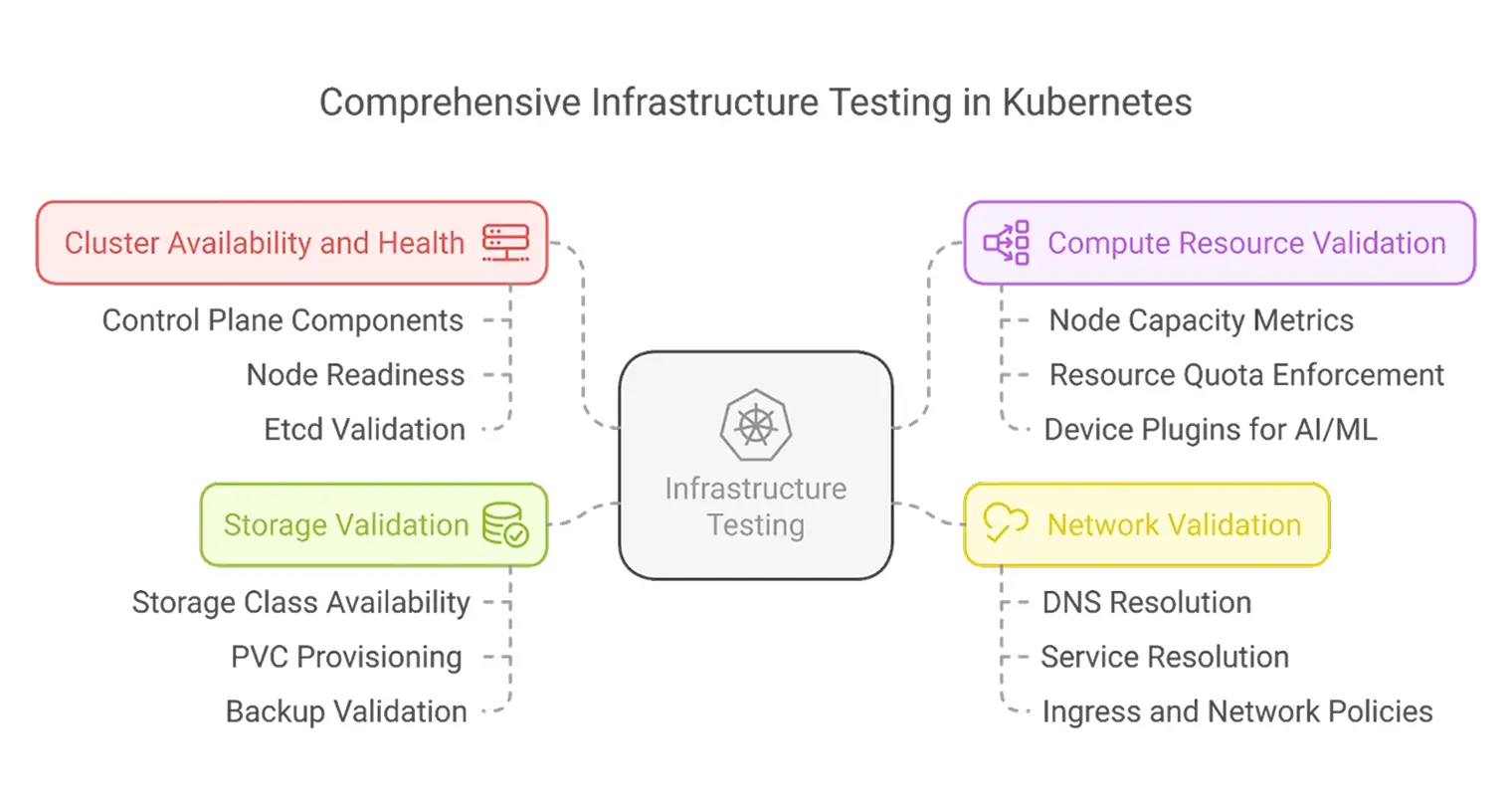
- Target specific infrastructure layers. Validate cluster health (API server, etcd, CoreDNS), compute resources (CPU, memory, GPU availability), networking (DNS resolution, ingress routing, network policies), and storage (PVC provisioning, I/O performance, backup integrity).
- Trigger tests where they matter. Run validations from CI/CD pipelines, on Kubernetes events via webhooks, on cron schedules, or manually before critical deployments.
- Review results in one place. All test outputs, logs, and artifacts flow into the Testkube dashboard. Use AI-assisted analysis to surface patterns and root causes across failed infrastructure checks.
- Act on findings. Use results as quality gates to block deployments, trigger remediation workflows, or flag configuration drift before it reaches production.
What you can validate
Cluster Health
Verify API server responsiveness, node readiness, etcd health, and CoreDNS status. Catch control plane degradation before it impacts workloads.
Compute Resources
Confirm node capacity, resource quota enforcement, and device plugin availability for specialized workloads like GPU/TPU. Validate that pod scheduling rules (affinity, taints) are functioning correctly.
Networking
Test DNS resolution, service routing (ClusterIP, NodePort, LoadBalancer), ingress rule processing, TLS termination, and network policy enforcement. Verify load balancer health probes and traffic distribution.
Storage
Validate storage class provisioners, PVC provisioning and access modes, I/O throughput and latency under load, snapshot and backup capabilities, and retention policy enforcement.
When to run infrastructure tests
- Pre-deployment: Validate cluster health before workloads are deployed
- Post-provisioning: After infrastructure changes via Terraform or CloudFormation
- Post-upgrade: Verify compatibility after cluster upgrades
- Scheduled intervals: Detect configuration drift with regular validation runs
- Before critical releases: Pre-flight checks before deploying high-impact workloads
Why Testkube
Traditional infrastructure testing approaches require managing multiple tools, custom integrations, and separate result aggregation. Each tool produces different output formats, runs in different environments, and stores results in different locations. Testkube eliminates this fragmentation.
- Kubernetes-native execution: Tests run as Kubernetes jobs inside your cluster, with access to internal services and accurate network conditions
- Tool-agnostic orchestration: Use curl, k6, pytest, Postman, or any containerized tool without building custom integrations
- Unified observability: Every test result, regardless of tool or trigger, lands in a single dashboard with log analysis, artifact storage, and historical comparison
- Quality gates: Configure Testkube as a gate in your deployment pipeline to enforce infrastructure validation before releases proceed
- Scale across environments: Run the same validations across dev, staging, and production clusters from one control plane
Get started
Curious how Testkube can help your team validate Kubernetes infrastructure with confidence?
Run any test, anytime, anywhere